With gaming as a multi-billion-dollar industry today, protecting games is more important than ever. Especially during the early release window when most sales are generated.
In the past decade, Denuvo has been the prime anti-piracy solution. The Irdeto-owned protection software managed to delay pirate releases seriously. Despite being a nuisance to many legitimate customers, gaming companies were pleased to pay for this first line of defense.
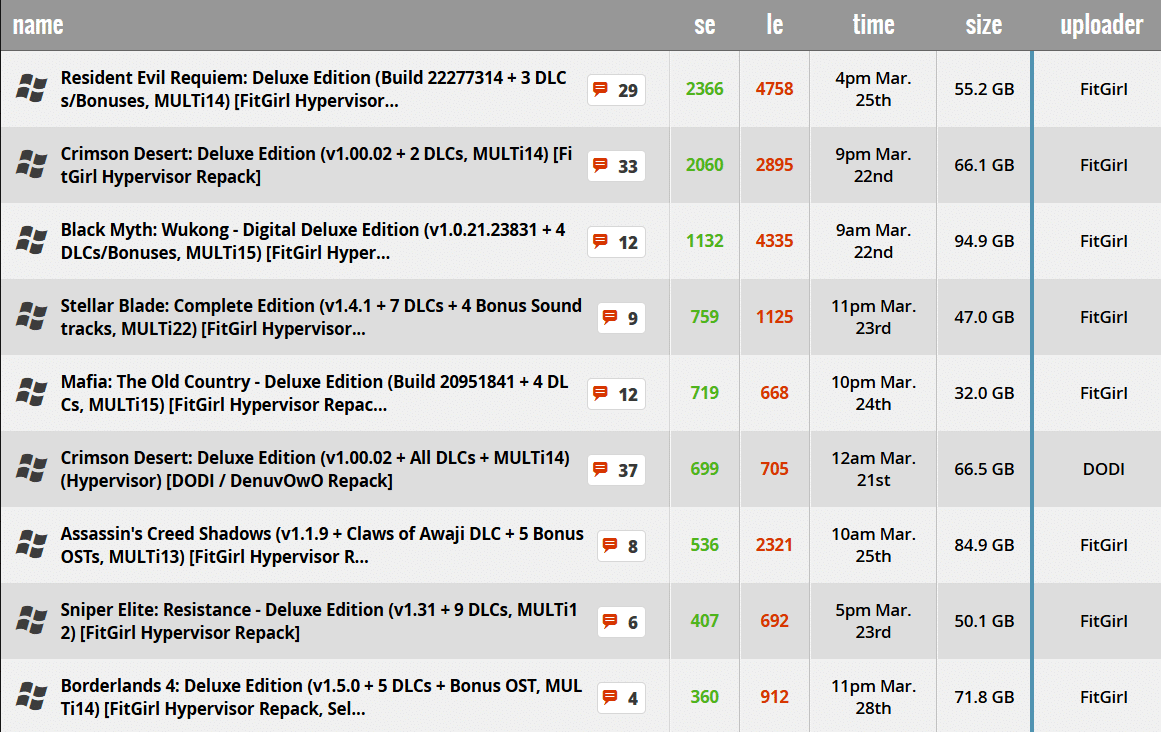
That is, until everything suddenly appeared to change a few weeks ago with the pirate leak of ‘Resident Evil Requiem,’ mere hours after its official release.
Hypervisor Bypasses Break Denuvo on Day Zero
The early leak was not a one-off. A wave of hypervisor-based Denuvo bypasses came out recently, including day-zero releases of major titles, including Crimson Desert and Life is Strange: Reunion. Meanwhile, long-protected titles like Assassin’s Creed Shadows also fell to the new method.
The speed and scale of the breaches, which also bypass other DRM software, are unprecedented. Where some reputable game crackers previously feared that Denuvo would effectively end game piracy, the tables have completely turned now.
Hypervisor leaks
Traditionally, crackers were required to reverse engineer Denuvo’s DRM paths to patch the game, which is a labor-intensive process that could take months.
Hypervisor bypasses take a fundamentally different approach. They don’t interfere with the game directly, but they operate beneath the operating system’s standard security visibility level, in what security researchers call Ring -1.
At this fundamental level, with key security features disabled, the hypervisor bypasses can intercept Denuvo’s CPU instructions and feed back false data to make the game believe that the tampering protection is still in place.
Because these bypasses are much easier to develop, these new ‘cracks’ come out faster than ever. Where pirates previously had to wait for weeks, they can now play pirated games within hours. That’s unprecedented.
Security Concerns
The hypervisor bypasses are a breakthrough, but they are not without concern. Right off the bat, critics warned that for them to work, pirates essentially have to turn off a key protection layer on their computer.
The bypasses are also plagued by hardware-specific problems and limitations that make them far from a simple patch. AMD systems are currently more stable, while Intel users face significant performance and stability issues, leading to other dangerous “tweaks”.
This cracking approach is still relatively young, and new developments surface nearly daily, with the game piracy forum Steam Underground (CS.RIN.RU) being a central hub.
The forum does not only facilitate pirate releases; it also offers detailed educational resources on potential security issues, warning that there are serious risks involved.
“[E]ven if you trust the authors of the hypervisor driver and even compile it yourself from source, a serious vulnerability in its code could instantly provide maximum and undetectable access to your system,” forum administrator RessourectoR writes.
One of the many warnings
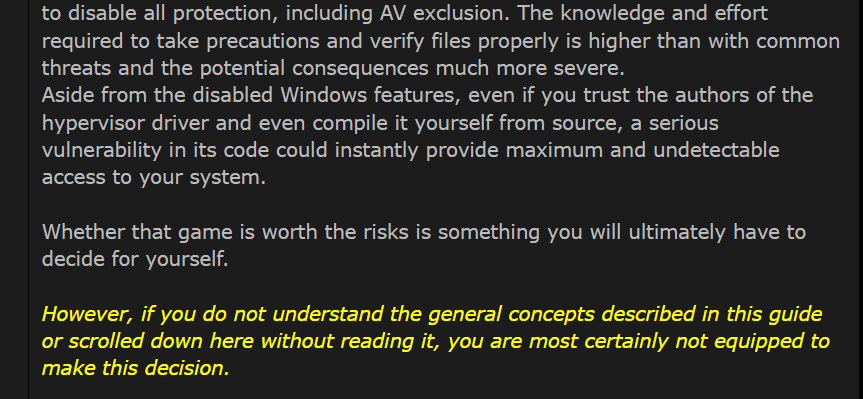
The question remains, of course, whether the average game pirate will read these warnings at all.
Denuvo’s Response
The scale of the bypasses has not gone unnoticed. While pirates try to navigate the security issues, Denuvo is working on an update that will counter the new hypervisor ‘cracks’.
Denuvo’s parent company, Irdeto, informs TorrentFreak that they are actively working on a countermeasure to address the Denuvo bypasses.
“We’re already working on updated security versions for games impacted by hypervisor bypasses. For players, performance will not be compromised by these strengthened security measures,” says Daniel Butschek, Irdeto’s head of communications.
Further details on these countermeasures will come out in due course. Some have speculated that to counter hypervisor cracks Denuvo would also has to operate in Ring -1, under the Windows kernel, but that is not the case.
“Addressing hypervisor-based workarounds will not require Denuvo to move into Ring -1 or deeper kernel level, and that is not the direction we’re pursuing,” Butschek says.
Denuvo
Since people in the pirate ecosystem already warn about security issues, it is no surprise that Irdeto also highlights these concerns.
“Hypervisor‑based bypasses rely on installing a custom, self-signed hypervisor that operates below the Windows kernel, giving it far broader control than a normal driver,” Butschek notes, warning that this makes systems more vulnerable.
“To run, users must disable major Windows security protections such as Virtualization‑Based Security (VBS), Hypervisor‑Enforced Code Integrity (HVCI) and driver signature enforcement, which are designed to prevent kernel‑level malware, rootkits, and ransomware.”
FitGirl Embraces Hypervisor Bypasses
Initially, popular game repacker FitGirl was also rather cautious due to the widespread security concerns.
“You won’t see any HV-cracks repacks from me until you won’t need to actually disable security features,” FitGirl wrote in an early post, adding that no game is worth the potential irrecoverable damage it can do to one’s computer.
However, as bypass development by KiriGiri and the broader MKDEV team continued, the security situation improved. When the requirement to disable Secure Boot or use the EfiGuard tool was eliminated, FitGirl shifted their position, while recognizing the drawbacks.
FitGirl began publishing hypervisor repacks shortly after, tagging each one visibly with a HYPERVISOR label and committing to replace them with traditional cracks if and when those become available.
Speaking with TorrentFreak, FitGirl further pointed to the ongoing technical improvements, while remaining cautious.
“The team behind those cracks is now working on maturing both the VBS.cmd part and the cracks themselves,” they told us. “So I think that most of the issues coming from Intel or older CPU will be resolved shortly.”
“Caution is still needed with hypervisor bypasses. Mostly for what you download and run. But that is true for any download; it is not hypervisor-specific,” FitGirl adds.
Strict Rules
FitGirl notes that people should never run anything on their computer until they’ve verified that it’s from a trusted source. This raises the question of whether one can trust semi-anonymous pirate sources, but for now no major incidents have been reported linked to hypervisor bypasses.
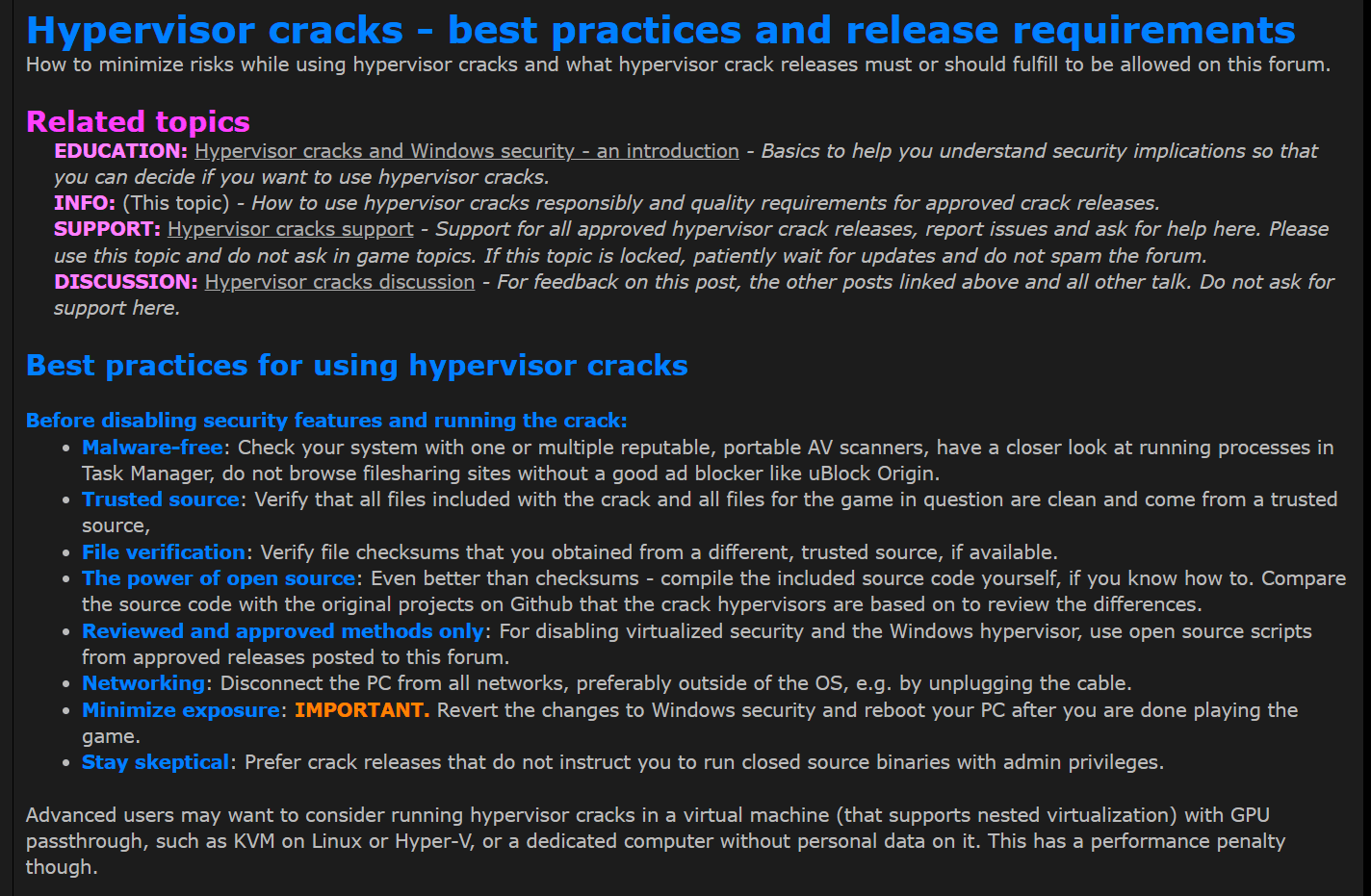
What stands out is the high level of community rules and moderation. CS.RIN.RU has always been very strict, and with these hypervisor bypasses, forum administrator RessourectoR maintains oversight through detailed release requirements and best practices.
Release requirements
According to FitGirl, these strict rules are reassuring. However, trust can always be broken in the future, and that’s also a risk here.
“Trust can be broken, yes, but we’re not there yet. And hope we won’t, considering how strict rules for publishing those cracks on CS.RIN.RU now are,” FitGirl tells us.
The Cat-and Mouse Game Continues
While Irdeto has several options to respond, the exact countermeasures remain a question for now. Denuvo could check if third-party hypervisors are running by checking CPUIDs or measuring CPU latency, for example.
FitGirl suggested that Irdeto can also respond by shifting to daily license ticket checks, but that would be a nuisance to legitimate players while it may also be bypassed. Alternatively, the company might ask Microsoft for help by restricting Driver Signature Enforcement (DSE) mode, but that doesn’t seem viable either.
One thing is for certain: Denuvo will try to tackle the problem as best as they can, continuing the seemingly endless cat-and-mouse game. While Irdeto knows that it can’t defeat piracy, it would like to go back to the situation where games remained crack-free for weeks.
For now, however, the hypervisor bypasses have made Day-0 pirate releases a reality. For those who are willing to take the risk.
From: TF, for the latest news on copyright battles, piracy and more.
Continue reading...