Welcome to World of IPTV
Join us now to get access to all our features. Once registered and logged in, you will be able to create topics, post replies to existing threads, give reputation to your fellow members, get your own private messenger, and so, so much more. It's also quick and totally free, so what are you waiting for?
Forum Rules
Our Rules: Read to avoid getting banned!
Advertising
Introduce Yourself to the World with Us!
Resource Database
Find the newest resources around IPTV!
Account upgrade
Upgrade your account to unlock more benefits!
You are using an out of date browser. It may not display this or other websites correctly.
You should upgrade or use an alternative browser.
You should upgrade or use an alternative browser.
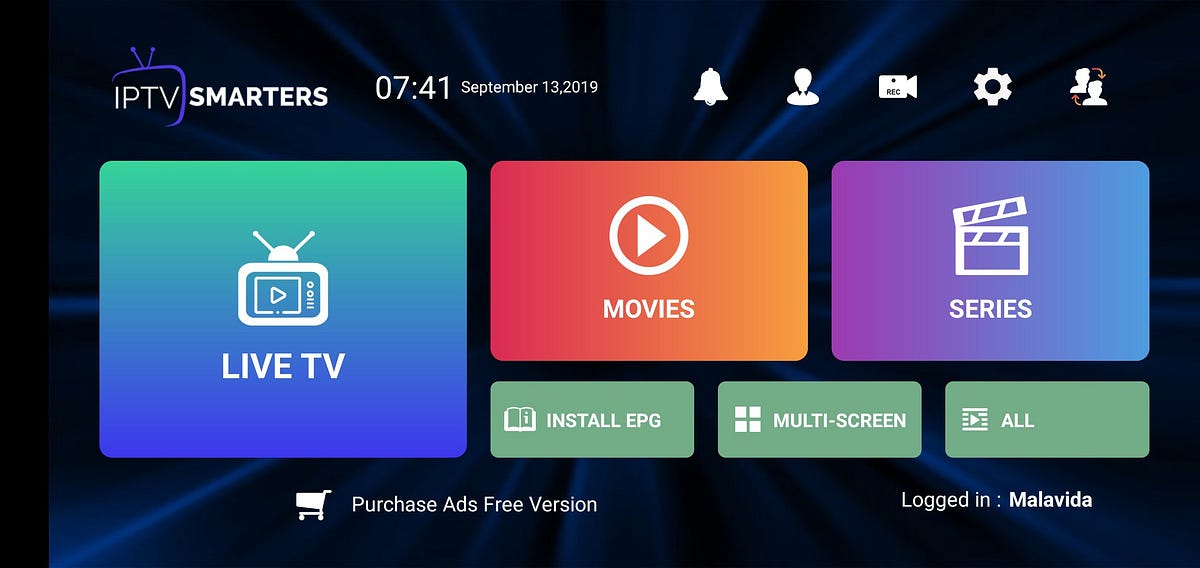
Info IPTV Smarters Exploit: CVE-2020–9380
- Thread starter darkvil
- Start date
Hello,
IPTV Smarters Exploit
be careful with this application this can affect your server (( destroy / steal ))... see the concept of theft:
No quote
No quote
Web Application Security, Testing, & Scanning - PortSwigger
PortSwigger offers tools for web application security, testing, & scanning. Choose from a range of security tools, & identify the very latest vulnerabilities.
| Channels | MatchTime Unblock CDN | Offshore Server | Contact |
| 100 cnx / 90€ | 5Gbps / 180€ | 48CPU-256GRAM 10Gbps 569€ | Skype live:giefsl |
| 500 cnx / 350€ | 10Gbps / 350€ | 48CPU-128GRAM 5Gbps / 349€ | TG @changcdn |
| 1000 cnx / 500€ | 20Gbps / 700€ | 40CPU-128GRAM 20Gbps / €980 | http://coronaserver.com |
The absolute state of this code
This will have been 0dayed for a long time, the quality of development is so so bad with iptv. That will accept any file from anyone. Ridiculous.
PHP:
session_start();
if (file_exists("functions.php")) {
include_once "functions.php";
if (isset($_FILES["logoImage"])) {
$target_dir = "../images/";
$target_file = $target_dir . basename($_FILES["logoImage"]["name"]);
if (move_uploaded_file($_FILES["logoImage"]["tmp_name"], $target_file)) {
echo "images/" . $_FILES["logoImage"]["name"];
exit;
}
echo "errorImage";
exit;
}
...This will have been 0dayed for a long time, the quality of development is so so bad with iptv. That will accept any file from anyone. Ridiculous.
Certainly! my friend. Those responsible for the smarters contacted me and informed that it is one without many problems. They don't really know anything.The absolute state of this code
PHP:session_start(); if (file_exists("functions.php")) { include_once "functions.php"; if (isset($_FILES["logoImage"])) { $target_dir = "../images/"; $target_file = $target_dir . basename($_FILES["logoImage"]["name"]); if (move_uploaded_file($_FILES["logoImage"]["tmp_name"], $target_file)) { echo "images/" . $_FILES["logoImage"]["name"]; exit; } echo "errorImage"; exit; } ...
This will have been 0dayed for a long time, the quality of development is so so bad with iptv. That will accept any file from anyone. Ridiculous.
Certainly! my friend. Those responsible for the smarters contacted me and informed that it is one without many problems. They don't really know anything.
Ahh, the man himself. Nice job on the exploit, good to see it properly reported as CVE. Hopefully smarters will do something now it's getting picked up in the tech news.
| Channels | MatchTime Unblock CDN | Offshore Server | Contact |
| 100 cnx / 90€ | 5Gbps / 180€ | 48CPU-256GRAM 10Gbps 569€ | Skype live:giefsl |
| 500 cnx / 350€ | 10Gbps / 350€ | 48CPU-128GRAM 5Gbps / 349€ | TG @changcdn |
| 1000 cnx / 500€ | 20Gbps / 700€ | 40CPU-128GRAM 20Gbps / €980 | http://coronaserver.com |
Yep, tried it and it worksAdded a patch:
No quote
How can we be sure that this patch is safe to use?Added a patch:
No quote
As you joined the forum 6 months ago
and only have 1 post which is this patch
| Channels | MatchTime Unblock CDN | Offshore Server | Contact |
| 100 cnx / 90€ | 5Gbps / 180€ | 48CPU-256GRAM 10Gbps 569€ | Skype live:giefsl |
| 500 cnx / 350€ | 10Gbps / 350€ | 48CPU-128GRAM 5Gbps / 349€ | TG @changcdn |
| 1000 cnx / 500€ | 20Gbps / 700€ | 40CPU-128GRAM 20Gbps / €980 | http://coronaserver.com |
How can we be sure that this patch is safe to use?
As you joined the forum 6 months ago
and only have 1 post which is this patch
Hi Mobilehacks,
6 months of forum, but the creator of the CVE and the exploit.
10 years in google hall of fame for security:
You don't have to trust me if you don't want to, the patch source is open.
But I think I'm the wrong person to have questions about, I would personally rather question the IPTV Smarters quality.
Nothing personal intended i was purely just asking a questionHi Mobilehacks,
You don't have to trust me if you don't want to, the patch source is open.
But I think I'm the wrong person to have questions about, I would personally rather question the IPTV Smarters quality.
| Channels | MatchTime Unblock CDN | Offshore Server | Contact |
| 100 cnx / 90€ | 5Gbps / 180€ | 48CPU-256GRAM 10Gbps 569€ | Skype live:giefsl |
| 500 cnx / 350€ | 10Gbps / 350€ | 48CPU-128GRAM 5Gbps / 349€ | TG @changcdn |
| 1000 cnx / 500€ | 20Gbps / 700€ | 40CPU-128GRAM 20Gbps / €980 | http://coronaserver.com |
It is not new that IPTV Smarters does not expire confidence. At least for me ...
Now it has only been exposed in the media.
Roger that!
João br?
This would be a good solution instead of removing the snips, if not please correct if im wrong.
PHP:
<?php
//Vulnerability 1: Arbitrary File Upload
if (isset($_FILES["logoImage"])) {
//added to check file extentions
$file_ext=pathinfo($_FILES['logoImage']['name']);
$extensions= array("jpeg","jpg","png","JPEG","JPG","PNG");
if(in_array($file_ext,$extensions)=== false){echo 'Not a valid file ext.';die("Error")}
//end of check
$target_dir = "../images/";
$target_file = $target_dir . basename($_FILES["logoImage"]["name"]);
if (move_uploaded_file($_FILES["logoImage"]["tmp_name"], $target_file)) {
echo "images/" . $_FILES["logoImage"]["name"];
exit;
}
echo "errorImage";
exit;
}
//Vulnerability 2: Code Injection
if (isset($_POST["action"]) && $_POST["action"] == "installation") {
//check to see if form data came from same REFERER
if ((isset($_SERVER['HTTP_REFERER']) && !empty($_SERVER['HTTP_REFERER']))) {
if (strtolower(parse_url($_SERVER['HTTP_REFERER'], PHP_URL_HOST)) != strtolower($_SERVER['HTTP_HOST'])) {
die("Error")
}
}
//end check
$response["result"] = "no";
$content = "<?php \n";
$content .= "\$XCStreamHostUrl = \"" . $_POST["HostUrlVal"] . "\";" . "\n";
$content .= "\$XClogoLinkval = \"" . $_POST["logoLinkval"] . "\";" . "\n";
$content .= "\$XCcopyrighttextval = \"" . $_POST["copyrighttextval"] . "\";" . "\n";
$content .= "\$XCcontactUslinkval = \"" . $_POST["contactUslinkval"] . "\";" . "\n";
$content .= "\$XChelpLinkval = \"" . $_POST["helpLinkval"] . "\";" . "\n";
$content .= "\$XClicenseIsval = \"" . $_POST["licenseIsval"] . "\";" . "\n";
$content .= "\$XClocalKey = \"" . $_POST["LocalKey"] . "\";" . "\n";
$content .= "\$XCsitetitleval = \"" . $_POST["sitetitleval"] . "\";" . "\n";
$content .= "?>";
if (file_exists("../configuration.php")) {
unlink("../configuration.php");
}
$fp = fopen("../configuration.php", "w");
fwrite($fp, $content);
fclose($fp);
chmod("../configuration.php", 511);
if (file_exists("../configuration.php")) {
$response["result"] = "yes";
}
echo json_encode($response);
exit;
}
?>This would be a good solution instead of removing the snips, if not please correct if im wrong.
PHP:<?php //Vulnerability 1: Arbitrary File Upload if (isset($_FILES["logoImage"])) { //added to check file extentions $file_ext=pathinfo($_FILES['logoImage']['name']); $extensions= array("jpeg","jpg","png","JPEG","JPG","PNG"); if(in_array($file_ext,$extensions)=== false){echo 'Not a valid file ext.';die("Error")} //end of check $target_dir = "../images/"; $target_file = $target_dir . basename($_FILES["logoImage"]["name"]); if (move_uploaded_file($_FILES["logoImage"]["tmp_name"], $target_file)) { echo "images/" . $_FILES["logoImage"]["name"]; exit; } echo "errorImage"; exit; } //Vulnerability 2: Code Injection if (isset($_POST["action"]) && $_POST["action"] == "installation") { //check to see if form data came from same REFERER if ((isset($_SERVER['HTTP_REFERER']) && !empty($_SERVER['HTTP_REFERER']))) { if (strtolower(parse_url($_SERVER['HTTP_REFERER'], PHP_URL_HOST)) != strtolower($_SERVER['HTTP_HOST'])) { die("Error") } } //end check $response["result"] = "no"; $content = "<?php \n"; $content .= "\$XCStreamHostUrl = \"" . $_POST["HostUrlVal"] . "\";" . "\n"; $content .= "\$XClogoLinkval = \"" . $_POST["logoLinkval"] . "\";" . "\n"; $content .= "\$XCcopyrighttextval = \"" . $_POST["copyrighttextval"] . "\";" . "\n"; $content .= "\$XCcontactUslinkval = \"" . $_POST["contactUslinkval"] . "\";" . "\n"; $content .= "\$XChelpLinkval = \"" . $_POST["helpLinkval"] . "\";" . "\n"; $content .= "\$XClicenseIsval = \"" . $_POST["licenseIsval"] . "\";" . "\n"; $content .= "\$XClocalKey = \"" . $_POST["LocalKey"] . "\";" . "\n"; $content .= "\$XCsitetitleval = \"" . $_POST["sitetitleval"] . "\";" . "\n"; $content .= "?>"; if (file_exists("../configuration.php")) { unlink("../configuration.php"); } $fp = fopen("../configuration.php", "w"); fwrite($fp, $content); fclose($fp); chmod("../configuration.php", 511); if (file_exists("../configuration.php")) { $response["result"] = "yes"; } echo json_encode($response); exit; } ?>
FireTvGuru The file Upload code is good, that's a perfect solution.
But the second one, it will be easy to be exploited, because anyone can spoof the Referer. The best solution would be having an installation script that gets removed after executed.
| Channels | MatchTime Unblock CDN | Offshore Server | Contact |
| 100 cnx / 90€ | 5Gbps / 180€ | 48CPU-256GRAM 10Gbps 569€ | Skype live:giefsl |
| 500 cnx / 350€ | 10Gbps / 350€ | 48CPU-128GRAM 5Gbps / 349€ | TG @changcdn |
| 1000 cnx / 500€ | 20Gbps / 700€ | 40CPU-128GRAM 20Gbps / €980 | http://coronaserver.com |
Thank you for your work.Added a patch:
No quote
Similar threads
- Replies
- 0
- Views
- 145
- Locked
- Replies
- 1
- Views
- 343
- Replies
- 2
- Views
- 521
- Replies
- 0
- Views
- 144
- Replies
- 0
- Views
- 333
About Us
Welcome to World of IPTV. With +23k members +13k threads +115k posts we are the most popular IPTV community on the web.
We have often been copied, but our copies only make us stronger!
We have often been copied, but our copies only make us stronger!
Quick Menu
Online statistics
- Members online
- 5
- Guests online
- 2,089
- Total visitors
- 2,094
- Robots
- 77
Totals may include hidden visitors.